Protecting your applications from
hackers is hard
They are always looking for that backdoor or insecure password to wreak havoc. And you’ve spent a lot of time and money on your applications, so you don’t want that hard work ruined in a matter of minutes.
If a malicious hacker managed to gain access to your application, they could deface the site, capture client information, or hold it all for ransom. You could face losing clients and money. Your brand name could be damaged.
The worst-case scenario means losing your business entirely (many small to mid-size businesses don’t have the money to deal with a breach, causing them to file for bankruptcy).

That’s where we come in.
We are the good (ethical) hackers. We’ll test your apps as an unethical hacker would and let you know what we find. Some findings may be provided in real-time so you can work on addressing them right away. That way you can sleep well at night, knowing that you’ve done your due diligence and your clients will be happy purchasing a secure app.
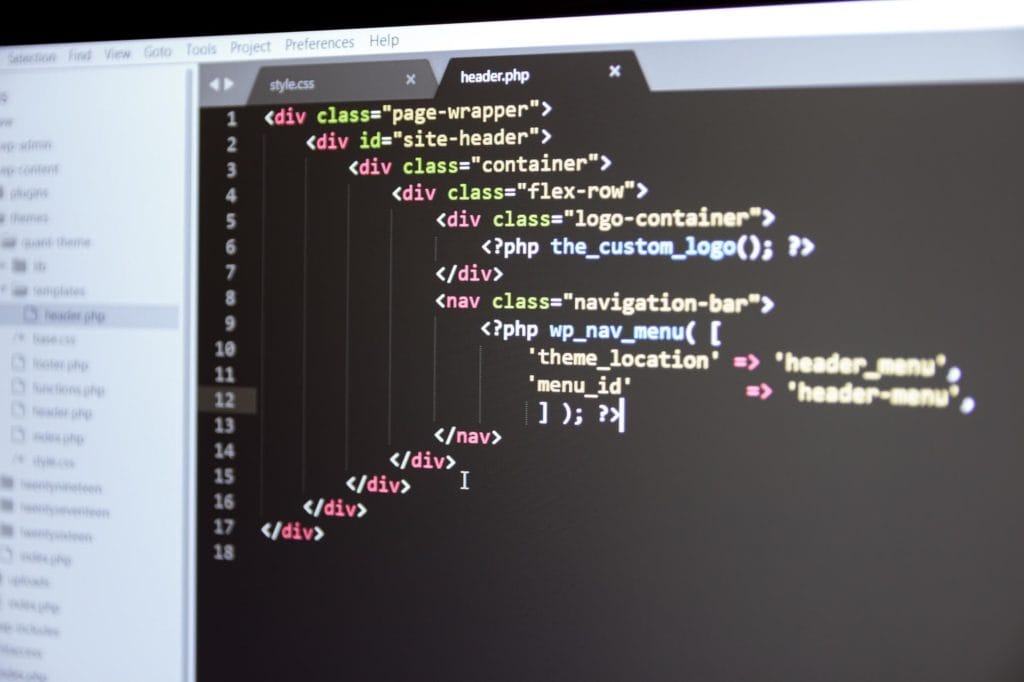
Web Application
Using the OWASP® Testing Methodologies, we provide the best in comprehensive penetration tests.
- Injection Tests
- Insecure Communication Methods
- Improper Error Handling
- Improper Access Controls
- Session Management
- Improper Authentication
- Authorization Management
- Outdated or Vulnerable Software Versions
- Input Validation
- Circumvent Workflows

Application Programming Interface
- Improper authorization
- Input validation
- Message integrity
- Weak authentication
- Output encoding
- Broken authentication/ session management
- Cryptography
- Data encryption HTTP return code
Mobile Application
- User experience
- SQL injection
- SSL validation
- Session hijacking
- Data leakage
- And more

Nobody likes to part with
their hard-earned cash
That’s why you deserve a company that works with integrity to give you the best bang for your buck.
- Testing provided since 2002 with 1000s of happy customers
- Penetration testing performed by certified, US-based cybersecurity experts
- Information gathered during testing remains in the US
- Manual testing means your assigned tester(s) won’t just push a button and walk away
- Experienced testers will help reduce the possibility of downtime during testing
- A la carte options so you can get a penetration test tailored to your company’s needs
- Simplified pre-test scoping and guidance when necessary
- Quick turnaround on pricing proposal
- Delivery manager to walk you through the process and answer questions
- Dedicated tester(s) who provide(s) information on vulnerabilities as they are discovered
- Exploitation of vulnerabilities as proof of severity
- Comprehensive report with:
- Executive summary
- Technical findings
- Screen captures
- Remediation recommendations
- Risk ratings
- After test debrief when requested
- Ready to work with a company that has your back? Fill out the form below.
MainNerve
Certifications
- Certified Ethical Hacker (CEH V6/V9)
- Certified Network Defender (CND)
- Certified Information Systems Security Professional (CISSP)
- eLearnSecurity Web application Penetration Tester (eWPT)
- GIAC Web Application Penetration Tester (GWAPT)
- Offensive Security Certified Professional (OSCP)
- Offensive Security Wireless Professional (OSWP)
- Offensive Security Web Expert (OSWE)


